Have you ever wondered about the planes flying overhead? What airline they belong to? Where they're going? Well, wonder no more! With the help of ADS-B (Automatic Dependent Surveillance-Broadcast), you can track flights in your area using a simple software package called dump1090-mutability. And the best part? You can do it all from the comfort of your own Linux machine. In this step-by-step installation guide, we'll show you how to get started.
Step 1: Installing dump1090-mutability
The first step is to install dump1090-mutability on your Linux machine. We'll assume that you're running Ubuntu or Debian, but the installation process should be similar for other Linux distributions. Open a terminal window and enter the following command:
$ sudo apt-get update $ sudo apt-get install dump1090-mutability rtl-sdr
Step 2: Running dump1090-mutability
Now that you've installed and configured dump1090-mutability, it's time to run it. Open a terminal window and enter the following command:
$ sudo dump1090-mutability --interactive
This will start dump1090-mutability and display the ADS-B data from nearby aircraft in real-time.
Step 3: Viewing Metric Units
By default, dump1090-mutability displays the output in imperial units. If you prefer metric units, you can use the following command instead:
$ sudo dump1090-mutability --metric --interactive
This will display the ADS-B data in metric units.
Conclusion -
Tracking flights with ADS-B using dump1090-mutability is a fun and educational project that can be easily accomplished with a Linux machine. By following this step-by-step installation guide, you'll be able to view the ADS-B data from nearby aircraft and learn more about the planes flying overhead. So why not give it a try? Who knows what kind of interesting flights you'll discover!
Also Read -
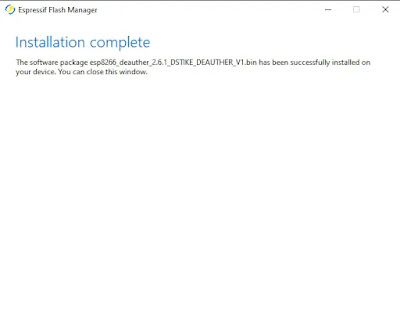
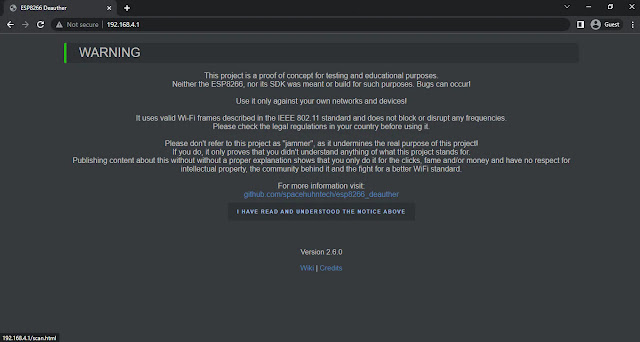
How to create a ESP8266 Wi-Fi Deauthenticator in just $4
DIY WiFi Repeater with an ESP8266: A step by step Guide
How to Secure Your Linux System by Adding a Bootloader Password














.png)
.png)







